The Ultimate Guide: How to Use the Global Fraud Index to Educate Your Team About Current Scam Threats
In the rapidly evolving digital landscape of 2026, the velocity of information often exceeds our systemic ability to comprehend it. For corporate leaders, IT professionals, and security teams, this presents an existential threat. The nature of fraud has undergone a structural transformation; your enterprise is no longer dealing with lone-wolf hackers or static email campaigns. Today, we face highly agile, algorithmic syndicates that orchestrate dynamic operations and pivot with lightning speed.
By the time a novel phishing technique or a sophisticated invoicing scheme makes it into your company’s quarterly security compliance module, the criminals have already extracted their value and moved on to a new target. This fundamental misalignment—the gap between the speed of fraud execution and the speed of corporate awareness—creates an asymmetric battlefield. Defenders are consistently playing a desperate game of catch-up.
This is where the Civoryx Global Fraud Index changes the math.
This comprehensive, step-by-step tutorial will teach you how to leverage the Civoryx Index not just as a passive data dashboard, but as a dynamic educational tool to protect your team, empower your employees, and eliminate the “Latency Problem” of traditional cybersecurity training.
The Philosophy: Understanding the “Latency Problem”
Before you can educate your team, you must understand why traditional training fails. The creation of Civoryx was sparked by a realization that our current threat intelligence data is dangerously late.
When a new scam variant launches, a victim’s first instinct isn’t to call the IT department or file a police report. It is to search the internet:
- “Is this text message real?”
- “Geek Squad renewal invoice $499”
- “EZ Pass scam text 2026”
This spike in search queries represents the very first measurable indicator that a new scam is scaling. It is the “smoke” before the “fire.” Traditional fraud reporting works in reverse. Agencies like the FTC or FBI aggregate loss reports over months, eventually publishing a bulletin. By the time you incorporate that bulletin into your team’s training, the scam has reached its saturation point, and the perpetrators have shifted their infrastructure to a new lure.
What does Civoryx say? “Fraud evolves faster than headlines. To stop fraud, we must track the curiosity and confusion of the potential victim in real-time. By tapping into the global search patterns of billions of people, the index provides a real-time lens into the queries that dominate the collective consciousness regarding digital deception.”
The Engine: How Civoryx Monitors, Measures, and Scores
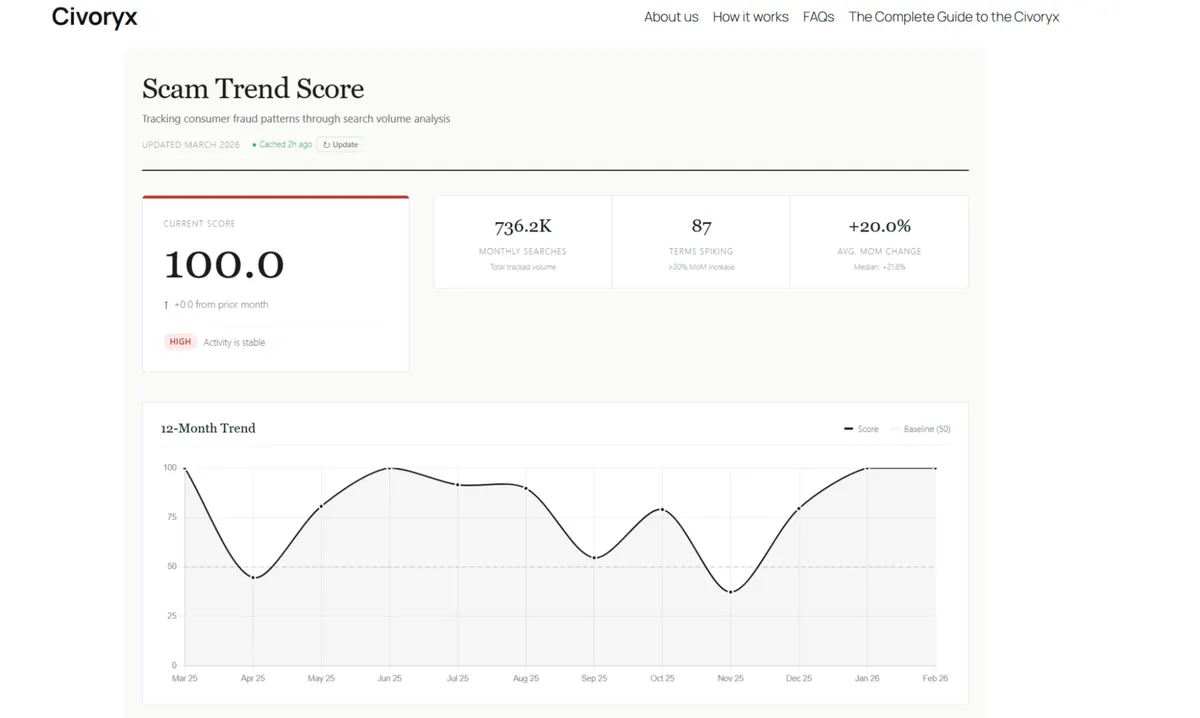
To effectively teach your team how to use this tool, you must be able to explain how it works. The Civoryx Index is built on a tripartite mathematical structure that distills millions of data points into a single, digestible metric: the Scam Trend Score.
1. Monitor: The 150 Keyword Taxonomy
The foundation of Civoryx is a meticulously maintained directory of over 150 fraud-related search terms. This is a living taxonomy that spans the entire spectrum of modern fraud, including social engineering, P2P banking, infrastructure impersonation, and emerging tech.
2. Measure: Weighted Month-Over-Month Velocity
Raw search volume can be misleading. For instance, the word “phishing” will always have high volume. If it increases by 5%, it is notable but expected. However, if a niche term like “EZ Pass Scams” jumps from 100 searches to 8,000, that is a 7,900% increase—a clear signal of a viral, coordinated attack.
3. The Unique Advantage: The 90-Day Recalibration Model
What makes Civoryx the definitive barometer for your team’s training curriculum is its adaptive nature. Civoryx recalibrates its keyword weighting model every 90 days. Why is this crucial for your training? Because scammers are economically motivated “unregistered entrepreneurs.” They abandon tactics that no longer yield a high return on investment (ROI). By recalibrating the weighting model every 90 days, Civoryx ensures that the “Scam Trend Score” is never artificially inflated by legacy searches. Your team is always looking at a refined, highly accurate reflection of the current quarter’s threat landscape.
4. Score: The Scam Trend Score
The final output is the Scam Trend Score. A rising score indicates that fraud-related search interest is accelerating globally. A falling score suggests that scam activity is cooling off. For context, in the February 2026 snapshot, the aggregate Scam Trend Score reached a staggering 226.68, fueled by a total volume of 794,880 fraud-related searches (a 33% MoM increase).
Step-by-Step Tutorial: Educating Your Team with Civoryx
Now that you understand the underlying mechanics, here is how you can practically integrate the Civoryx Global Fraud Index into your organization’s security awareness culture.
Step 1: Replace Annual Training with “Just-in-Time Security Awareness” (JIT-SA)
Traditional corporate security training is often ignored because it feels theoretical and disconnected from daily work. Civoryx allows IT and management teams to implement “Just-in-Time” training based on active, measurable threats.
How to Execute This? Instead of sending a generic “Watch out for scams” email once a quarter, check the Civoryx Index every Monday morning. Look at the keyword velocity to see what is trending.
- The Scenario: You notice that while general “Phishing” queries are stable, searches for “Geek Squad Scam” and “PayPal Scam Email” have surged by 514% and 308%, respectively.
- The Translation for Your Team: These specific types of scams represent “Refund Fraud” and “Invoice Lures,” which are incredibly dangerous for corporate finance and operations departments. An employee might see a fake Geek Squad renewal for $499, panic, and call the “support number” in the email, leading directly to a remote-access takeover of their workstation.
- The Action: Send an immediate, targeted alert to your Finance and Operations teams. Include a screenshot of the Civoryx data showing the 514% spike.
- The Result: Because the data is empirical, current, and quantified, employees take it seriously. The surprise factor is removed. You have transformed theoretical risk into a tactical, real-world warning.
Step 2: Teach the “Personal Smoke Test” for SMS Phishing
One of the most valuable ways to use Civoryx is to empower your employees to protect themselves on their mobile devices. The line between personal and professional devices is blurred, and a compromised employee phone is a risk to the enterprise.
You need to teach your team how to use the index as a real-time verification engine to combat “Smishing” (SMS Phishing).
How to Execute This? Run a 10-minute workshop demonstrating how to handle high-urgency text messages. Use the “EZ Pass” anomaly of early 2026 as your primary case study.
- The Scenario: Show your team a sample text: “Urgently: Your vehicle has an unpaid toll violation for EZ PASS. Failure to pay within 24 hours will result in a $50 fine and license suspension. Pay here: [malicious link].”
- The Psychological Trap: Explain that scammers use infrastructure impersonation because it triggers a flash of panic.
- The Civoryx Solution: Instruct your team that instead of clicking the link, their new reflex should be to visit the Civoryx Index and check the Keyword Velocity table. Show them the real data from February 2026:
| Keyword | Jan Volume | Feb Volume | % Change |
| EZ Pass Scams | 140 | 8,100 | +5,685.7% |
| Toll Scam Text | 130 | 3,200 | +2,361.5% |
| DMV Scam Text | 230 | 3,200 | +1,291.3% |
What is The Lesson? Teach your team that a 5,600% statistical explosion is the fingerprint of a massive, botnet-driven campaign. By seeing that thousands of other people are searching for the exact same term simultaneously, the employee moves from a state of fear (believing they are personally targeted) to a state of logic (recognizing a mass campaign). They can delete the message with absolute confidence.
Step 3: Map Seasonal Surges to Departmental Vulnerabilities
Scammers relentlessly exploit the calendar. They know when people are waiting for W-2s, tax refunds, or holiday packages, and they adjust their scripts accordingly.
How to Execute This? Use the index to track seasonal trends and preemptively educate your Human Resources and Accounting teams.
- The February Snapshot Case Study: In February 2026, the Civoryx index captured a massive migration of search intent toward IRS impersonation. Searches for “Tax Fraud” jumped from 8,100 to 74,000—an 813.58% increase. This single keyword contributed 75.74 points to the overall Scam Trend Score.
- The Action: Before Q1 ends, hold a brief alignment meeting with HR. Show them the Civoryx contribution metrics. Warn them that attackers will be heavily targeting employees with spoofed emails requesting payroll diversions or W-2 data.
Step 4: Address the “Halo Effect” of Brand Impersonation
Scammers leverage the trust consumers have in major brands to bypass critical thinking. Civoryx aggregates searches to rank which companies are being most heavily exploited.
How to Execute This? Review the “Big Three” most impersonated brands with your procurement and vendor-management teams. Based on the 2026 data, these are:
- PayPal: 51,800 searches (Primarily “PayPal scam email” and “PayPal fraud”).
- Chase: 18,100 searches (Primarily “Chase fraud number”).
- Coinbase: 12,100 searches (Primarily “Coinbase text scam”).
- The Action: If your business utilizes PayPal for vendor transactions or Chase for corporate banking, you must establish “High-Alert” protocols. Educate your team that if they receive an urgent communication from these specific brands, the statistical likelihood of it being fraud is currently peaking. Mandate a secondary verification method (like calling a known, internal vendor phone number) before processing any unexpected invoices from these platforms.
Step 5: Prevent “Awareness Fatigue” by Tracking Scam Decay
For teams with limited time and resources, knowing what not to talk about is just as important as knowing what to highlight. Employees suffer from “awareness fatigue” if you constantly warn them about every possible threat under the sun.
How to Execute This? Use the “Cooling Trends” (negative velocity) data in the Civoryx Index to retire outdated training modules.
- The Scenario: You are preparing a monthly security newsletter. You traditionally include a warning about gift card scams.
- The Data Check: You check Civoryx and note that “Gift Card Scam” queries have dropped by 45.70% (because retailer point-of-sale awareness campaigns are working). Similarly, the “McAfee Scam” has dropped by 45.45%, and the “Brushing Scam” is down 18.68%.
- The Action: Remove these legacy threats from your current training rotation. Pivot your entire presentation to focus on the emerging threats that are actually surging, such as the 816% jump in “Coinbase text scams” or AI voice cloning.
- The Result: By following the negative velocity in the index, you ensure your educational efforts are always focused on the “Rising Tide” of fraud rather than the “Receding Wave.” This respects your employees’ time and makes your training exponentially more effective.
Step 6: Integrate Civoryx Data into Product and UI/UX Development
If your company builds software, fintech applications, or e-commerce platforms, educating your internal development team on how to use Civoryx is a game-changer.
How to Execute This? Teach your Product Managers and UI/UX designers to use the index as a dynamic API for user friction.
- The Concept: Security pop-ups annoy users. But what if your app only deployed friction when global threat levels were high?
- The Application: If your company processes P2P payments, have your developers monitor the open data feed. If “Zelle Scams” or “Payment Request Fraud” spikes by 400% on Civoryx, trigger a “High-Alert” state in your app’s code. Automatically enable an extra confirmation screen for users sending money to a new contact.
- The Result: When the index shows that P2P fraud is cooling, the app reverts to a frictionless experience. You have effectively taught your development team to build a “Smart Security” layer that responds dynamically to the real-world fraud environment.
Civoryx is A Free Tool for Everyone
You might be wondering how to justify the budget for this level of threat intelligence. The beauty of the Civoryx Global Fraud Index is that in an era where cybersecurity feeds are often sold for tens of thousands of dollars, it remains 100% free.
There are no paid tiers, no premium accounts, and no paywalls. The philosophy behind Civoryx is simple: Fraud transparency should not have a price tag. Cybercriminals do not discriminate based on budget; they target the intern and the CEO with equal aggression. By keeping the data open and public, Civoryx ensures that the strongest weapon against fraud—collective visibility—is democratized.
Conclusion
Educating your team about cybersecurity is no longer about teaching them to look for typos in an email or hovering over a URL. With AI-generated lures and deepfake audio becoming the norm, the traditional signs of a scam are vanishing.
You must shift your team’s mindset from analyzing the content of a threat to analyzing the context of a threat.
The Civoryx Global Fraud Index provides that context. It is a real-time map of the digital battlefield. By relying on aggregate human behavior, utilizing a 90-day recalibration model for peak accuracy, and turning raw search volume into actionable intelligence, you can build a workforce that is natively resistant to digital deception.
When fraud shifts, the world is searching. Teach your team to watch the smoke, and you will never get burned by the fire.